Infrastructure as Code (IaC) in ops0 lets you define, deploy, and manage cloud infrastructure using declarative configuration files. Write code with AI assistance, validate with policies, estimate costs, and deploy with approval workflows.
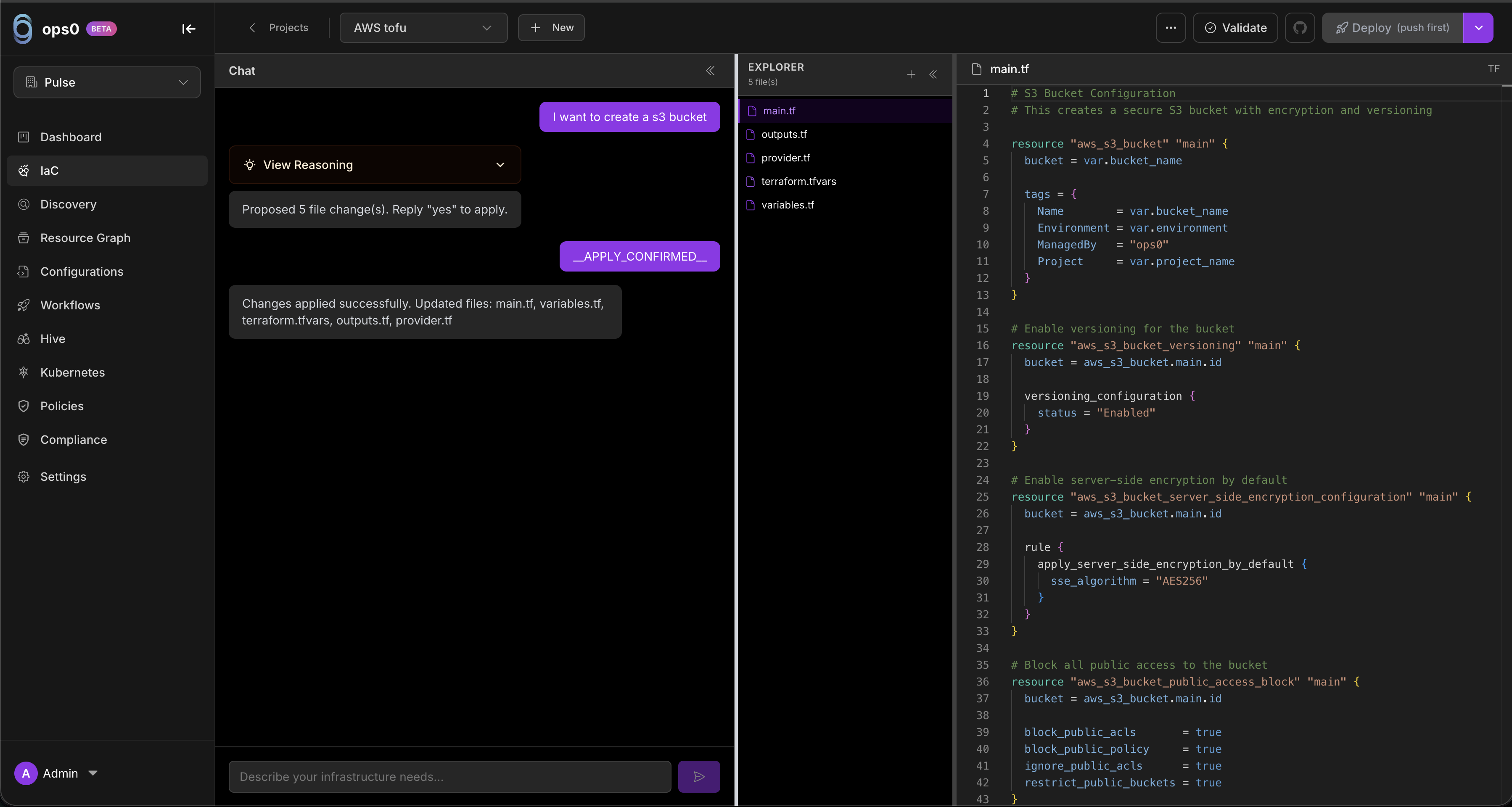
Write Terraform code from natural language. Describe what you want, get production-ready code.
Automatically check security and compliance before deployment. Block violations.
See monthly cost estimates before you deploy. No surprises on your cloud bill.
Two-way sync with your Git repositories. Edit in ops0 or your IDE.
Choose your IaC engine (Terraform, OpenTofu, Oxid, or CloudFormation). Pulumi support is upcoming. Configure the state backend and cloud provider.
Use the editor or ask AI to generate infrastructure code.
Preview changes before applying them. See resource additions, modifications, and deletions.
Automatic security and compliance validation against mapped policies.
Review estimated monthly costs for planned infrastructure changes.
Apply changes with optional approval workflows and scheduling.
| Engine | Status | Description |
|---|---|---|
| Terraform | Available | HashiCorp's infrastructure provisioning tool |
| OpenTofu | Available | Open-source Terraform fork, fully compatible |
| Oxid | Available | Rust-based IaC engine |
| Pulumi | Upcoming | Infrastructure in TypeScript, Python, Go, or C# |
| CloudFormation | Available | AWS-native infrastructure templates with change sets and StackSet support |
Describe infrastructure in plain English and get production-ready code:
"Create a VPC with public and private subnets,
NAT gateway, and proper security groups for a
3-tier web application"
The AI produces complete, best-practice Terraform code with proper naming, tagging, and security configurations — for example:
# main.tf — VPC with public/private subnets and NAT gateway
resource "aws_vpc" "main" {
cidr_block = "10.0.0.0/16"
enable_dns_hostnames = true
enable_dns_support = true
tags = {
Name = "my-app-vpc"
Environment = "production"
ManagedBy = "ops0"
}
}
resource "aws_subnet" "public" {
count = 3
vpc_id = aws_vpc.main.id
cidr_block = cidrsubnet(aws_vpc.main.cidr_block, 4, count.index)
availability_zone = data.aws_availability_zones.available.names[count.index]
map_public_ip_on_launch = true
tags = {
Name = "public-subnet-${count.index + 1}"
Tier = "public"
}
}
resource "aws_subnet" "private" {
count = 3
vpc_id = aws_vpc.main.id
cidr_block = cidrsubnet(aws_vpc.main.cidr_block, 4, count.index + 3)
availability_zone = data.aws_availability_zones.available.names[count.index]
tags = {
Name = "private-subnet-${count.index + 1}"
Tier = "private"
}
}
resource "aws_internet_gateway" "main" {
vpc_id = aws_vpc.main.id
tags = { Name = "my-app-igw" }
}
resource "aws_eip" "nat" {
domain = "vpc"
}
resource "aws_nat_gateway" "main" {
allocation_id = aws_eip.nat.id
subnet_id = aws_subnet.public[0].id
tags = { Name = "my-app-nat" }
}
data "aws_availability_zones" "available" {}
Schedule deployments for specific times or recurring intervals:
| Mode | Description |
|---|---|
| Immediate | Deploy now (default) |
| Scheduled | Deploy at a specific date and time |
| Recurring | Deploy on a cron schedule (e.g., daily, weekly) |
Scheduled deployments run plan + apply at the configured time with all policy checks enforced.
Replicate an existing IaC project across cloud providers or regions:
Choose the project to replicate.
Select the target cloud provider, region, and account.
View estimated costs for the replicated infrastructure before proceeding.
ops0 produces adapted Terraform code for the target environment.
The Replication Wizard supports cross-cloud replication (e.g., AWS to GCP) with intelligent resource mapping.
Visualize Terraform variable and resource dependencies as a directed acyclic graph (DAG):
ops0 scans IaC code for security vulnerabilities using Checkov:
Before deploying, see estimated monthly costs:
| Resource | Type | Monthly Cost |
|---|---|---|
| EC2 Instance | t3.large | $60.74 |
| RDS Database | db.r5.large | $172.80 |
| NAT Gateway | per hour | $32.40 |
| Total | $265.94 |
Multiple team members can work on the same project simultaneously:
Save project configurations as reusable blueprints:
Require approval before deployments execute:
Each project stores Terraform state in a configured backend:
| Backend | Description |
|---|---|
| S3 | AWS S3 bucket with optional DynamoDB locking |
| Azure Blob | Azure Storage Account |
| GCS | Google Cloud Storage |
Navigate to the IaC section in the sidebar.
Click the + New Project button.
Name the project, select Terraform (or another engine when available), and configure the state backend.
In the editor, use AI to generate code: "Create an S3 bucket with versioning enabled"
Review the code, click Plan, review the output, then Apply.
ops0 extends beyond IaC authoring and deployments. These capabilities work alongside your IaC projects:
Detect when live infrastructure drifts from your IaC state across AWS, GCP, and Azure.
Enforce compliance with OPA/Rego policies evaluated against Terraform plans and deployed state.
Scan existing cloud resources and generate IaC code to bring them under management.
Manage Ansible playbooks and Kubernetes manifests with AI-driven configuration projects.
Build multi-step pipelines with triggers, approval gates, and parallel execution.
Visualize cross-project dependencies and blast radius across your IaC projects.
Create, manage, and organize IaC projects.
AI-powered code editor with autocomplete.
Save and reuse project templates.
Plan, apply, and schedule infrastructure changes.
Two-way sync with Git repositories.
Manage sensitive values for deployments.
Variable graphs, replication, and advanced features.